Article/Document:
Deceptive UFO Documents: Doubt, Debate and Daunting Questions
International Space Sciences Organization Research, November 25, 1999
original source | fair use notice
Summary: Briefly summarizes early findings of ISSO's ongoing research into the authenticity of the so-called "MJ-12" documents concerning the U.S. military's alleged recovery of extraterrestrial spacecraft in the mid-1900s.
Foreword
The following document briefly summarizes early findings of ISSO's ongoing research into the authenticity of the so-called "MJ-12" documents concerning the U.S. military's alleged recovery of extraterrestrial spacecraft in the mid-1900s.
In the quest to better understand a phenomenon defined as Unidentified, researchers have over the years specialized into diverse and sometimes conflicting domains of study related to the UFO enigma. Inquisitive students unfamiliar with the history of such research - rich as it is in interpretation - can often be shocked and intimidated by the extent of materials to consider reading. It can be very hard to identify the most important veins of writings to consider. The first book one is likely to pick up relates yet another experiential story with circumstantial reporting - tough to accept as sufficient evidence for a transformation of worldview. Thus many rational, intelligent people who might otherwise be persuaded to think differently do not ever find their way to the most important research, and reject the entire UFO question is irrelevant fantasy.
We find ourselves in this circumstance partly because of the lack of a tree of dependency for the various hypotheses circulating as currency within the UFO debate. What aspects of alleged UFO phenomena depend upon validity of what other aspects? What are the root questions that shape the tree of answers in print? What ideas in UFO research are most central for us to consider?
A possible structure of such a tree of dependency can be organized as follows, each category of question more fundamental than the next.
Have unidentified objects been observed flying about in our atmosphere?
What is the simplest model capable of integrating the observations with existing science?
What other predictions does the model offer beyond the observed phenomena itself?
How might our future change if such predictions are valid?
What aspects of the phenomena may have been studied in secret?
My own answers to the first, second, third, and fourth order questions are: (1) UFOs have been witnessed by tens of thousands of people, (2) the scientific revolution fits hand-in-glove with the trajectory of leading-edge physics, suggesting significant corrections to early-20th century assumptions, (3) experimental studies are now revealing new secrets of Nature appearing to confirm these corrections, and (4) the possible near-term transformative effects upon humanity could be extremely large.
In this context, containment of extraterrestrial technology by a compartmentalized body of humans is not hard to imagine, but the question of the authenticity of certain documents alleging such is a fifth order question. It is therefore not in my mind the primary driver of any of the most vital answers we seek to UFO phenomena. It is simply one of many fascinating and important tributaries of a raging, rising river of ontological revolution.
All things considered, and acknowledging substantial dependence upon first and second hand interviews with highly reputable individuals, I presently hold the belief that a quasi-governmental body maintains substantial non-public information and very possibly physical materials related to the UFO phenomenon. If this belief turns out to be false, then (1) there has been a startlingly extensive intelligence effort aimed at convincing certain people and nations that we have such materials, and (2) the anomaly research community, as tattered a bunch as it is, is in fact at the arrowhead of one of the most important revolutions in human history, with no government body better informed on the UFO question.
Granting real extraterrestrial UFO phenomena for a moment, the realization that governing bodies have no superior secret knowledge of it would be almost as surprising as learning of actual hardware recovery. Yes, even the fifth order questions in this domain are important to consider.
Having thus set for forth my view of the category of question into which the authenticity of any of the MJ-12 documents falls, the status of ISSO's review of the MJ-12 documents is described in the body of this report.
-------------------------------------------------------------------------------
The MJ-12 Documents
updated March 20, 2000
Deception in statecraft is a widespread practice not limited to any one theme nor provenance, not confined to any specific period of history nor to only a few countries and governments. For obvious reasons, it is a practice little revealed and rarely discussed. Were much said, it would be ineffective and would, therefore, soon cease. Deception is widely practiced by military and intelligence organizations of many countries on a broad scale throughout history.
Deception in statecraft has been variously defined, never with certainty. One imminent scholar of its recent history, Charles Cruickshank (1979), says that deception is the art of misleading an enemy into doing something or not doing something so that his strategic or tactical position will be weakened.
Once it becomes even more obvious that all of the so-called MJ-12 documents were officially fabricated as instruments of U.S. covert psychological warfare, beginning in 1950 during the most threatening period of the Korean War, extending into at least the first Nixon Administration, the daunting question arises: what then; what next? It no longer matters that there never was a widely-accepted definition and practice of psychological warfare, whether covert or overt, during the early Cold War; what matters is the issue of official falsification in relation to ufology in general.
For example, does the psychological warfare clarification, striking on its own terms, mean that the whole history of governments' involvements with UFO crash recoveries, however construed, is suspect? Intriguing questions stem from a realization that the MJ-12 documents, both the earlier ones and the later ones, were or may have been contrived to mislead foreign, inimical (usually Communist or once-Communist) governments. For instance, were UFO crash recoveries staged for the same purpose, augmented by subsequent foistings of clever but deceptive, official-appearing documents to persuade adversaries that the U.S. might enjoy certain unique advantages gotten from recovering and studying crashed UFOs? Indeed, have there been any actual such exploitations and technology transfers as has been contended by some claiming to have been insiders? Is it all something else, secretive and important, but not ufological?
It is not the objective of such questions to impune the motives and methods of covert operations. Guilt by association is an ineffective form of criticism. When major, rival powers possess nuclear weapons, deception is a small price to pay to avoid nuclear war. It is much preferred to try to misdirect or mis-cue weapons research and development than to decide controversies with weapons themselves. Any workable theme of deception is ridiculously cheap by comparison with the alternatives.
Rather, an objective is to question not just the documents but the extent to which the UFO phenomenon is understandable and creditable when based on reflections of it that involve policies and practices of governments.
Covertly fabricated deceptive documents are genuine in the sense of being created by security and intelligence organizations to appear to be authentic and realistic in order to convince skeptical, foreign intelligence experts and political leaders to accept them as genuine and to alter their perceptions and behaviors accordingly; yet, the content information of such documents is carefully contrived to frighten, misconstrue and confuse target audiences. Serious, deliberate trade-offs are considered in such matters: what and how much of what truths to tell in what ways to convey artful fictions as if they were facts.
This covert tradecraft is endemic in the history of statecraft and is not unique to a UFO-related theme. It is as old as official documentation itself. For example, some 3,400 years ago, Hittite King Mursili II discovered that his temple officials, his keepers of the kingdom's rituals, records and official knowledge, had falsified certain wax-tablet recorded instructions in order to alter solemn, religious practices of crucial importance. Mursili II took immediate security remedy and had the proper, authentic instructions re-recorded on hard clay tablets (in lieu of by re-useable wax tablets) to preclude future instances of official document deception.
Deceptions, little or never coming to light, are ever-present thorns in the sides of historians, journalists and intelligence organizations. Because no one knows how many times he or she has been successfully deceived, the potential effects of deceptions, often promoted by documents, on any scientific research and development program is immeasurable and, even if nominally, of great consequence. Early Cold War nuclear and other weapons development programs, together with the development of means and methods to collect and evaluate scientific, technical and political intelligence, would have been susceptible to the information contained in several MJ-12 documents.
If one notices and accepts a host of irregularities and alterations of all of the MJ-12 documents as indicative of a covert psychological warfare operation then the deception cannot be adjusted, explained away, trivialized, excused or denied, neither of the earlier nor of the later documents surfaced between 1984 and 1999 by Shandera, Moore and Cooper. In terms of the techniques of questioned document examination, all of the documents are in some respects persuasive and convincing while in other ways dubious and suspicious. In general, they make verifiable sense chronologically, stylistically, typographically and in terms of separately-researched historical and organizational contexts. They also make sense in terms of various artifacts of the originals faithfully transformed by xerographic and film copying processes. Many of them show signs of having been film-copied by microfilming or video filming.
Document examination and authentication is a science of expert opinion; so are other sciences, generally probabilistic, but document examination is an empirical not a statistical science. There is no criterion for how many of what kinds of flaws determine inauthenticity. Historiographers, faces inevitable problems of remoteness from document sources and must make peer-acceptable adjustments for that gap. Adjustments include learning the details of the governing milieu of any questioned document according to its puted or imputed date. It is spurious to argue that fabricators and forgers strive for blemish-free reproductions whereas real bureaucrats composing altogether genuine documents make casual mistakes both in drafts and in edited finals. Such an argument would be discriminating only in an errorless world. Some errors are casual; others are not; indeed the difference often is a matter of expertise.
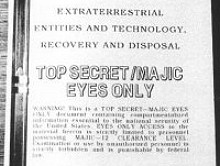
Of the many examples among the MJ-12 documents of such expert discernment is the cover page of the SOM 1-01 document by itself. Despite and apart from any debate about the authenticity of its contents, and caveats (or lack of them), the cover alone reflects irregularities of presented data not consonant with its contents and its date. Among these is that the expansion and derivation of its technical order nomenclature denotes subject material having nothing to do with the contents of the document. By itself this would make the document suspicious were it not for precedents of Soviet deceptive fabrications of U.S. military field manuals during the Cold War. (The USAF technical order (TO) identifier is of Korean War vintage and denotes operating instructions for airborne psychological warfare equipment.)
Withal, the MJ-12 documents are professionally, artfully crafted, good enough to fool informed, perceptive analysts. In that quality, the documents are not the work of amateurs or casual hoaxers. They were not created for monetary profit but for national security purposes supplementary to larger, often crucial issues and goals. Nevertheless, each document, including the Eisenhower Briefing Document and its companion, the Truman-Forrestal Memorandum, also reveal often subtle indications of having been tradecrafted to the ends of covert psychological warfare. These include numerous flaws and alterations of content, administrative data, composition, style and original construction of which arguably the most interesting are anachronisms of state-of-the-art knowledge and of terms of reference and other elements of language peculiar to certain times and places. Some of these indicators thus far have escaped the published notice of critics.
A favorite of critics has been the word "retro-virus" in the questioned document called "lst Annual Report," undated but initially dated from its obvious content to some time in 1952; yet, "retro-virus" is a word not in either the technical nor the popular language before the early 1970s. Viruses characterized as "retro-grade organisms" by University of Minnesota Professor Robert Green in 1935 nor the normative term "retra-virus" suggested at a conference of cancer specialists in 1960 do not resolve the issue and must be regarded as futile attempts to explain away the obvious. What seems to have escaped the critics is that "retrovirus" appears in Russian medical literature in the late 1960s and might, therefore, be an apt word, a fearsome, threatening word, to incorporate into a deceptive U.S. psychological warfare document created during the same Cold War period.
Perhaps, then, 1st Annual Report is itself a fabrication, but does that condemn the others? This is an interesting question in terms of the modus operandi of historiographers to examine suspicious documents as individual pieces of a collection of documents, the principle of reinforcement either for or against authenticity. Of the instances of appearance in 1st Annual Report of the word "celestial," it is misspelled in half of those instances in precisely the same way in which it is, in all instances, misspelled in the questioned document called the Oppenheimer-Einstein draft essay dated June 1947, i.e., "celestrial," as in "extraterrestrial."
One of the more obvious machinations of six or seven of the MJ-12 documents is that their contents and style emulate those of other, known-authentic historical documents but of subject material having nothing to do with UFOs. These we may call the General-Twining-Mission-to-New Mexico documents of mid-1947 to conduct with a party of experts and officials an investigation of one or more crashed UFOs. These questioned documents emulate real, authentic documents concerning General Albert Wedemeyer's mission to China and Korea, also in mid-1947, to investigate the political, economic and military situations in those two countries then hotly contested by active Communist forces and influences. The emulations are by no definition parodies; rather, they are professional creations--a common practice in fabricating deceptive documents for purposes of covert psychological warfare based on the premise that nothing better conveys genuineness than does genuineness itself.
What critics who would claim common fraudulence in this particular instance omit to consider is that about three and one-half years after the Wedemeyer Mission, during the darkest days of the Korean War that Wedemeyer predicted in 1947, official records about U.S. China policy of the State Department's Far Eastern Affairs Bureau were collected and studied in private by the Secretary of State, Dean Acheson. It is a matter of official U.S. Department of Defense history that in late November 1950, Dean Acheson sanctioned covert operations against Peking and Pyongyang at a point in the history of U.S. national security when the Department of State was the leading practitioner and pace-setter, among all agencies, of psychological warfare.
Nevertheless, the emulation instance is but among several indicators across all of the MJ-12 documents of their having been tradecrafted to deceive Communist policy-makers and their intelligence people, no mean fakers themselves. Interestingly, at least one covert (and clandestine) intelligence cum diplomacy insider, the late Miles Copeland, told at least one leading UFO researcher, Timothy Good, that in the early 1960s, the CIA conducted covert, UFO-related deception operations against the Peoples' Republic of China to keep the Chinese off balance and persuade them that we were doing things that we were, in fact, not doing. (Good, 1996, Beyond Top Secret, p. 424.)
It is no secret over the last twenty to thirty years that there existed in the U.S. Government's executive branch an elaborate structure and function for conducting covert and overt psychological warfare against the Communist nations, part of larger capabilities, that included fabrication and foisting of genuine-appearing but deceptively-informing documents the themes of which varied as appropriate to desired ends. A variety of responsible histories published from at least the mid-1960s inform readers, often in verifiable, scholarly detail, of various aspects of the organization and activities of this extensive capability.
It is easy to trivialize and sensationalize this kind of thing, but as instruments of covert psychological warfare, the MJ-12 documents were made decades in the past to suit threats and other security issues of the times, particularly the early Cold War including the hot Korean War, now largely lost to living memory. Like all such deceptions, their perpetrators foresaw in them limited, temporal means and aims not intended to survive beyond their objectives. There always is uncertainty in such operations, which largely is why they are regarded as ancillary or supplemental to more concrete, overt policies and operations. The elements of risk of detection and of ineffective disseminations mean that covert psychological warfare operation should never be undertaken to carry the main weight of critical national security problem-solving.
Yet, how can we be sure that the MJ-12 documents remain questionable documents of overall authenticity; can we wrap up their original provenance one way or the other? In effect, we can. Assembling a body of experts to identity, collect and essentially characterize all issues and points of both whole genuiness and of genuiness distorted to the aims discussed above will produce two lists of approximately equal weight. Any such divided results ipso facto diminish whole genuineness argument while substantiating official strategem simply because all such deceptive documents are crafted to appear genuine and do, hopefully cleverly, blend, hopefully seamlessly, fact and fiction. Amateur fakers do not have the means and knowledge to fabricate documents as convincing as are most of the MJ-12 documents. There cannot be such contrast of pluses and minuses if the MJ-12 QDs are both genuine (officially made) and authentic (accurate and truthful as to content and administrative production.) In real document examination science, unlike in agriculture, there are no hybrids. In historical research of statecraft, fact and fiction mixed together is always deception, not just be definition but by practice and by logic.
That, however, is not end of the story but only its condition as we now find it. In view of the once-enacted psychological warfare operation (itself explicitly discussed in three of the documents, a fact that should alert even non-specialists) involving the MJ-12 documents, is the UFO phenomenon as a whole believable? Perhaps governments would surreptitiously lie about it to other governments, but what about independent world-wide sightings, abductions, contacts, electromagnetic interferences, altered terrain, radar cases, pilot encounters and the like--all of these apparently apart from official-looking documents?
What about the hundreds of pages of UFO-related governments' documents released to the public under provisions such as the U.S. Freedom of Information Act or of scheduled reviews and declassifications of not just the U.S. but of Britain, Russia, Spain, France and elsewhere? Are these officially-released documents questionable as well, even if not once part of covert operations? Is there an overall UFO documents pattern; if there is, what does it connote?
Before these individual manifestations of the UFO phenomenon in general can be allowed to contribute to any pattern, each must be substantiated or dismissed on its own merits. Not all that glitters is gold, but some glitter is from gold. Very few UFO researchers undertake the expensive, critical effort to differentiate among the obvious, the not-obvious and the deep or obscure manifestations of the whole UFO phenomenon.
Because of the relative ease of staging phoney UFO crash recovery operations, especially in little-populated, remote areas, witness accounts of such presumed events are a special case of differentiation and cannot be included among the spontaneous or extemporaneous manifestations. Witnesses to such events may believe what they experienced and may be convinced they are reporting what actually happened, but contrived UFO crash recovery operations can be staged with the same skill to the same end as deceptive documents fabricated and forwarded to strengthen and round out the overall ploy. Any reading of the history of the Bodyguard-Fortitude stratagem incident to D-Day, June 1944, (the Allied invasion of the European Continent,) will show how field-staging, deceptive documents, planted rumors and so forth all must be taken up together to be sufficiently persuasive.
In the end, daunting questions remain to be answered: What then, what next? Do the MJ-12 documents contain any truthful, reliable information about UFOs? What is it? Are any UFO crash recoveries valid events? Have any UFO technologies been exploited? Are UFOs all man-made; is the whole phenomenon, if distinctly its own, in some ways manipulated to conceal or disguise actual manageable projects? What is left creditable of the whole phenomenon? If any government, with great resources, goes to the extent and cost of staging phoney UFO crash recovery operations to mislead foreign intelligence collectors and contrives fabricated, official-appearing documents to buttress the impression, what is such a government really concealing or diverting attention from? All such operations, when they occur, are costly, troublesome, risky and uncertain; therefore, they obligate commensurate benefits or pay-offs. It is not a willy-nilly kind of thing casually undertaken and trivially compensated.
In any case, old, decrepit psychological warfare documents were "then;" questions they naturally raise are "now." Where do we go from here?
* * * * * * * * *
In a writing of this length, it is infeasible to cover the whole depth and breadth of the issue of the MJ-12 documents authenticity, as issue that never can be responsibly addressed apart from informed criticism and skepticism. Even in the best of circumstances, the many problems of the UFO-related questioned documents (QDs) do not yield to wistful reasonings and allowable excuses. The fact that the documents raise irremediable doubts is itself the best indication of their dubious origins. This pertains especially to the documents about Twining's 1947 mission to New Mexico that emulate genuine, authentic documents about Wedemeyer's 1947 mission to China and New Mexico.
It is a matter of record that from his service as Supreme Allied Commander in Europe in World War II, superintending the June 1944 invasion, General Eisenhower was particularly, personally interested in the complicated cover and deception operations enacted to divide and weaken the German defense.
It is a matter of record that later, when Eisenhower was U.S. Army Chief of Staff, some 16 days prior to the alleged crash and recovery of a UFO in New Mexico (June 16 and July 4, 1947 respectively) Eisenhower sent a memorandum to his director of plans and operations, Major General Lauris Norstad, directing that the War Department (which included the USAAF) take necessary steps to rejuvenate and keep vital "the arts of psychological warfare and of cover and deception ... in case an emergency arises."
It is a matter of record that the subsequent Army G-3 who replaced Norstad in the fall of 1947 and who took several steps thereafter to integrate psychological warfare into military planning was Lieutenant General Albert Wedemeyer.
It is a matter of record that in June 1947, the Army established an operating psychological warfare (PW) unit at Fort Riley, Kansas and began at Fort Riley's Army General School a course of instruction in PW.
It is a matter of originally secret record, declassified in 1952, that the recommendations and conclusions of the Air Force's (AMC) August 1949 Project GRUDGE report state that the UFO (flying discs) theme should be considered by Air Force headquarters' PW division for its potential in coordination with other agencies having PW missions (which included the Army, CIA and State Department) and that it also states that one prospect as seen by AMC/ATIC would be to combine the release of UFOs per se with the release of information about them. (Grudge's predecessor, Project SIGN's final report of December 1948 also discussed PW and flying saucers as one of four Soviet-related hypotheses.
It is a matter of fact that four of the questionable documents surfaced by Cooper explicitly discuss the prospect of UFO-centered psychological warfare vis-a-vis the Soviet Union.
It is a matter of opinion that some of the documents represent no device beyond office practice or classroom PW training exercises while others appear at least ready for operational introduction into foreign intelligence collection streams.
During the last quarter-century, many hundreds of pages of UFO-related governments' documents have been declassified and released to the public world-wide, in the U.S. often in response to FOIA requests. Their contents often are banal, not particularly breathtaking, as are the contents of the MJ-12 documents; nevertheless they are interesting. What such U.S. Government documents show collectively is that from 1944 through the 1960s, security, intelligence, foreign affairs and publicity agencies and offices were collecting data and information domestically and abroad and conducting studies simply to try to come to grips with the UFO phenomenon itself, to get their arms around it and understand it.
During this period of over twenty years, in the latter part of 1952, the released documents show that the Chairman of the covert operations panel of President Truman's National Security Council (a panel called the Psychological Warfare Strategy Board chaired by the Director of Central Intelligence) recommended to the PWSB and to the NSC (chaired by the President) that the UFO phenomenon be employed for psychological warfare purposes both offensively and defensively, in the same vein as had been recommended three years earlier by the Air Force's Project GRUDGE report.
There is no released documentation to the effect that this actually was done or not, though any such record would not be expected to survive in official history files; however, by 1957-1958 there occurs a subtle shift in the UFO data collection emphasis that began a dozen years earlier. What is seen from the released materials dated from at least 1957-58 to 1996 is a steady, unremitting, collection of information (intelligence) from several foreign countries, including Communist foreign nations, of these governments' and foreign publics' reactions to, impressions of, attitudes towards and military and political responses to the UFO phenomenon. One of the released documents shows that CIA began assessing Russian reactions to UFOs at the same time that the GRUDGE report recommended UFOs as a psychological warfare subject.
After approximately 1958 and more certainly after 1968, there was no longer data collection for the sake of phenomenological interpretations; rather, for the sake of assessing foreign neutrals and non-friendlies psychologies, sociologies and political attitudes about the UFO phenomenon. This is the marriage of psychological operations and intelligence, in the trade called "target studies."
There are in the UFO questioned documents several different terms of reference, acronyms, argots and ideas that simply were not extant in the American English language in 1947, some not until 1950, others not until 1959-60, still others not until the early 1970s. Such "fingerprints" are immutable: there are no ideas before their natural times in history.
Once all of the dubious MJ-12 documents are seen as examples, whether rudimentary or polished, of the tradecraft of deception in statecraft, all of their benefits and blemishes evaporate.
Read more articles on this topic: